A few days ago I got an email from HSBC Bank regarding my online Internet Banking account, saying that it was locked and that I could go down to a branch to unlock it or fill in the online form to unlock it. Initially I didn’t think much of it until I was about to go to HSBC and I decided to check whether my Internet Banking account was locked. I logged in without issue and grew suspicious of the email I had received earlier. I re-read email I found that it was a phishing email trying to steal my login credentials via the online form that was attached to the email. Below I will detail a few things that help you identify phishing emails or forms
Below is the received phishing letter and the accompanying update form. Now email with an attached form is always suspicious because you can never really trust anything you receive.


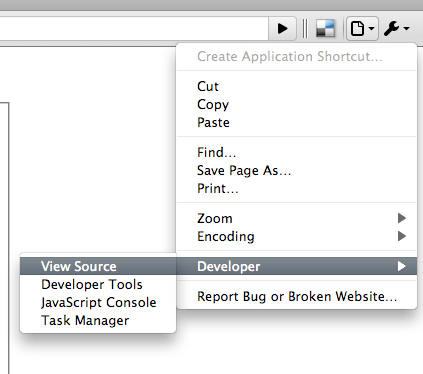
Now to inspect any HTML file or even a website you should always view the source code of the file. Search through the menu items and look for the “View Source” menu item. Below shows how to view source in Google Chrome (For Firefox: View > Page Source)
Viewing the source code will show you what makes up the webpage you are viewing. For any form that you fill in you should look for the “FORM” tag and in particular the “action” attribute/value as the “action” attribute/value dictates where the data will be sent. The screenshot below shows the source of the ‘Update Form’ attached to the email and as you can see the website that the data is being sent to (yuvalla.com) doesn’t seem to be a website that has anything with HSBC. Another thing to take note of is that the url has no “https” in the address that it is sending the form. All banking sites should be sending data via https (e.g. https://hsbc.com.bn/ibanking/processing.php not http://hsbc.com.bn/ibanking/processing.php) as HTTPS connections are encrypted (HTTPS server certificates must also be originating from a trusted source, e.g. the bank itself, in order to ensure that the encryption is between a trusted source and not a random malicious hacker’s computer/server).

Some other notifications that the email was suspicious:
- The phishing email “from” field is different from the regular HSBC “from” field (correct: HSBC Brunei, fake: HSBC Bank)

HSBC Phishing Email - Fake Name - The email they used does not original from HSBC.com or HSBC.com.bn (and going to the website gives a non-existent website)

HSBC Phishing Email - Fake Email
Note: these 2 notifications can actually be faked to look like the real thing and if they are correct they are not an indication that the email is authentic.
Ways to prevent being a victim of phishing emails
- Never blindly trust any emails you receive
- Do not fill in any forms without first checking it out properly (view source to make sure it is sending data to a trusted location, ensure https so the data is encrypted and cannot be sniffed)
- Do not click any links in an email as a link can display a URL direct you to another (e.g. http://google.com this link should go to Bing.com not Google.com)
- Manually type in the bank’s website to go to the Internet banking website (try using https in the address rather than http)
Now despite all this, there can always be security issues that enable hackers to exploit to make things even harder for us to identify fake websites / phishing emails. These tips are not a surefire way to ensure you do not get phished but hopefully the information I’ve shared will help you identify some characteristics of phishing emails so you can protect yourself and help inform others